Introduction:
From Cisco APIC version 6.0(2) onwards, it is possible to deploy a cluster with virtual APICs. This means that all three nodes in the cluster can be entirely virtual, marking a significant paradigm shift.
To achieve this, you can deploy a virtual APIC on AWS using the CloudFormation template or install a virtual APIC on ESXi servers using OVF in VMware vCenter.
The AWS model, which is currently available and actively used, is the same as the ESXi server option.
Note: Previously, the cluster had to be entirely physical, utilizing UCS hardware servers (3 Cisco UCS servers). Now, a combination of physical servers and virtual machines is possible, potentially reducing acquisition costs.
Configuration Options Two implementation modes are supported:
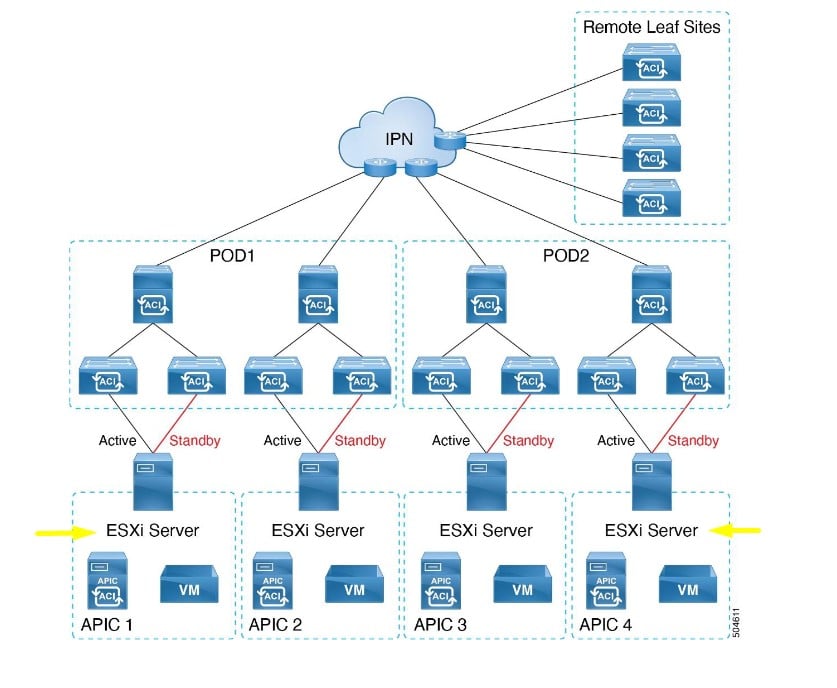
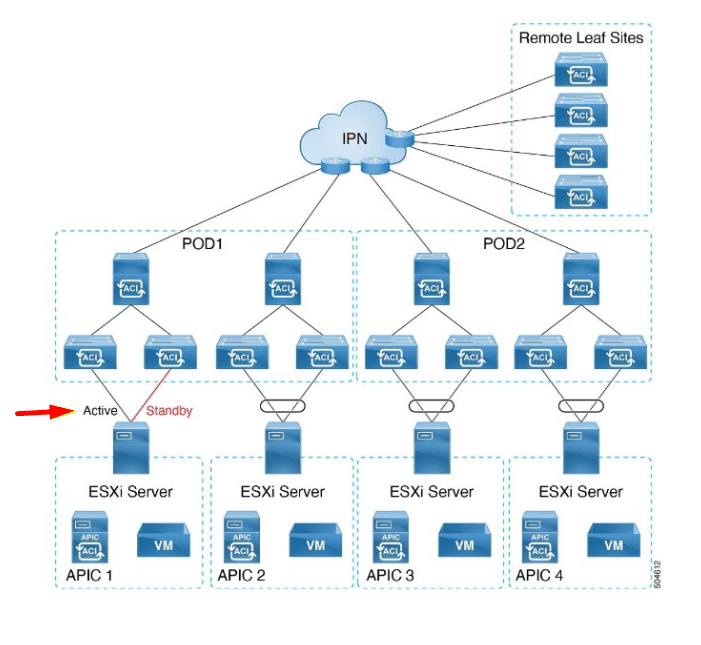
- All ESXi hosts on which virtual APIC(s) are installed are directly connected to the Leaf switches in the ACI fabric. ESXi servers can connect to Leaf switches using Standby-Active or Active-Active links with LACP Port-Channel. However, it is recommended that the ESXi server hosting APIC 1 uses only the Active-Standby mode.
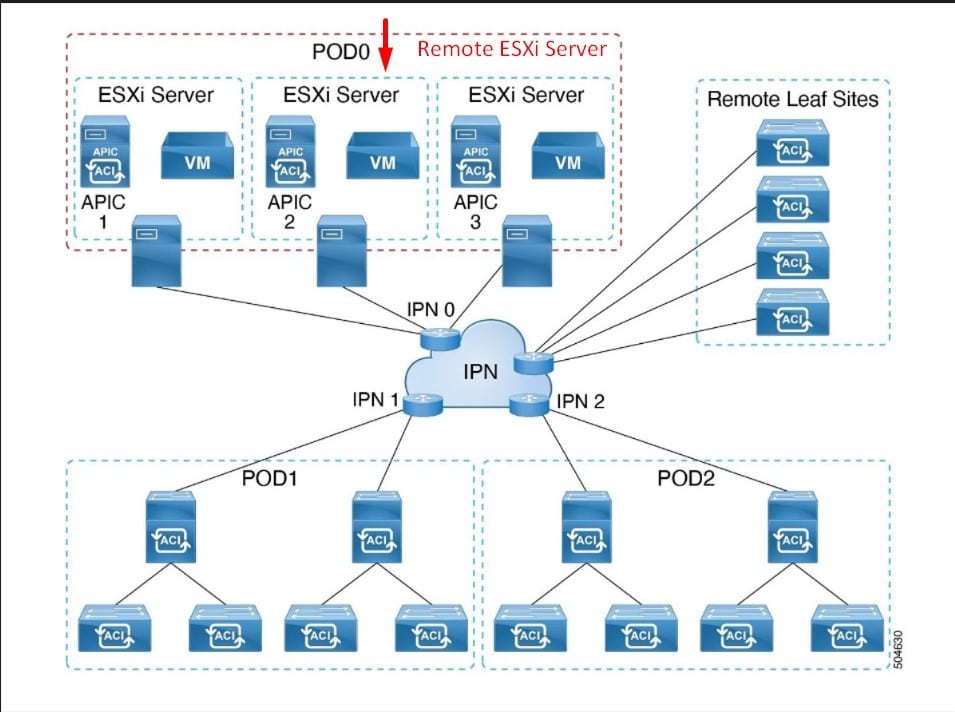
Implementation Option 2: The ESXi server hosting the installed virtual APIC(s) is remotely connected to the ACI fabric via an external network.
The virtual APICs are connected with Active-Standby links. As illustrated in the diagram below, virtual APIC machines are hosted on ESXi servers directly connected to Leaf switch(es). One of the uplink connections from the ESXi server to the Leaf switch is in Active mode, while the other is in Standby mode.
Note: LACP requires a Distributed Virtual Switch (DVS). LACP is not supported on a Standard Switch.
Note: For the cluster, APIC number 1 should connect with Active-Standby links. The other APICs in the cluster, from APIC 2 to N, where N is the size of the cluster, can be connected with Active-Active links.
The ESXi host is connected remotely to the ACI fabric. The virtual APIC machines are hosted on ESXi servers that are connected to the ACI fabric via an external network. These ESXi servers are connected remotely to the ACI fabric through an IPN (Inter-Provider Network).
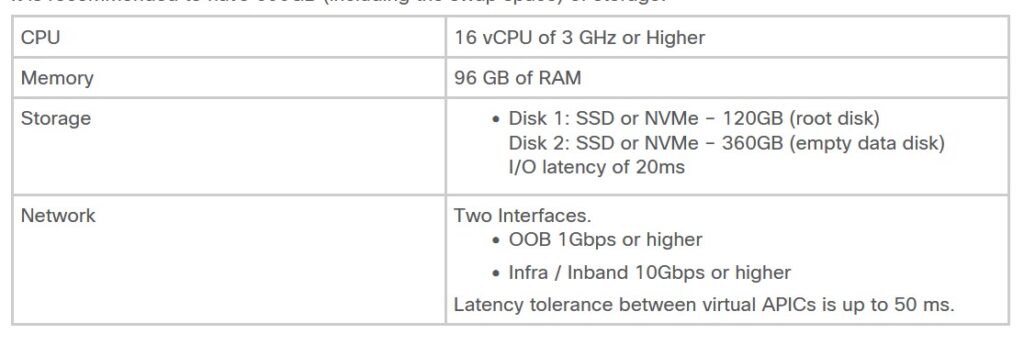
Prerequisites for Virtual Machines: ESXi servers must allocate the resources as per the table below for vAPICs. It is recommended to have a minimum of 600 gigabytes (including swap space) of storage available.
The virtual APIC cluster supports up to 1200 Edge ports and is compatible with processors, hard disks, and average memory.
Guidelines and Limitations for Installing Virtual APIC on ESXi:
- While supporting multiple virtual APICs on a single ESXi server is possible, for achieving high availability, it is recommended to install one virtual APIC on each ESXi host.
- Fabric switches must use ACI version 6.0(2) or later. Switches using versions prior to 6.0(2) can automatically upgrade their firmware to version 6.0(2) during Fabric Discovery through automatic firmware updates.
- Mixed mode support is not available; in other words, all APICs in a cluster should be of the same type (Layer 2 or Layer 3).
- Before installing virtual APICs on ESXi, ensure that the ESXi servers are synchronized with NTP.
- For consistent VMM extension on the same DVS used for hosting virtual APIC machines, enable CDP and disable LLDP in the Cisco APIC GUI.
- Connecting ESXi hosts through an intermediate switch, such as UCS Fabric Interconnects, is not supported.
- Standalone APIC support is not available in this configuration.
In the physical APIC cluster model, standalone APICs are automatically updated with firmware updates to ensure consistency with the active version in the cluster. This condition facilitates replacement in case of failure. However, in the virtual APIC cluster model, the user can create an instance of APIC with the required version.
For more information visit cisco official website https://www.cisco.com/c/en/us/td/docs/dcn/aci/apic/kb/virtual-apic/deploying-cisco-virtual-apic-using-esxi.html